Speak directly to the analyst to clarify any post sales queries you may have.
Positioning RBAC as a strategic pillar of enterprise security architecture that enables least-privilege, auditability, and governance across hybrid IT environments
Role-Based Access Control (RBAC) has ascended from a tactical IT control to a foundational component of enterprise security architecture, influencing how organizations govern identities, enforce least-privilege, and demonstrate compliance. This introduction frames RBAC not simply as a permissions mechanism, but as a strategic discipline that intersects identity fabric, application architecture, and operational governance. By situating RBAC within modern security paradigms-such as zero trust, identity-centric security, and cloud-first deployment strategies-organizations can better align access controls with business outcomes and regulatory expectations.
Over recent years, the proliferation of cloud-native applications, API-driven services, and distributed workforces has expanded both the attack surface and the complexity of access entitlements. Consequently, RBAC implementations are shifting from static role catalogs toward dynamic policy orchestration that integrates contextual signals and automated lifecycle management. This introduction explains the imperative for enterprises to modernize RBAC practices while preserving auditability and minimizing operational overhead.
This overview also delineates the relationship between RBAC and broader identity governance and administration (IGA) programs. It emphasizes the importance of clear role engineering, continuous role certification, and adaptable policy frameworks that span hardware, software, and service components. Finally, the introduction highlights the strategic choices organizations face-balancing on-premise legacy systems with cloud deployments, harmonizing vendor ecosystems, and prioritizing investments that yield rapid risk reduction-setting the stage for the detailed insights that follow.
How evolving zero-trust principles, automation, policy-as-code, and cloud-native integrations are reshaping RBAC architectures and enforcement practices in modern enterprises
The RBAC landscape is undergoing transformative shifts driven by technological innovation and evolving threat paradigms. First, the convergence of zero-trust principles with role-based models is prompting organizations to rethink long-standing assumptions about static role hierarchies; roles are being augmented by contextual attributes such as device posture, session risk, and geolocation to produce adaptive access decisions in real time. Consequently, access policies are migrating from manual spreadsheets and siloed directories to policy-as-code paradigms integrated with orchestration tooling.
Second, automation and machine learning are progressively applied to role lifecycle management. Automated role mining, behavioral analytics, and entitlement reconciliation are reducing the time and human effort required to maintain accurate role definitions, thereby lowering the incidence of privilege creep. At the same time, API-driven integrations are enabling tighter coupling between identity providers, cloud service providers, and enterprise applications, creating an environment where RBAC is enforced consistently across heterogeneous stacks.
Third, regulatory and compliance expectations are influencing RBAC design patterns. Organizations must demonstrate evidentiary trails for access provisioning and deprovisioning, and they are adopting continuous controls monitoring to meet audit demands. Additionally, the proliferation of cloud and hybrid deployments has elevated the importance of vendor interoperability and standards-based approaches that allow consistent enforcement regardless of the underlying infrastructure.
Finally, vendor offerings and deployment models are diversifying. Enterprises now select from combinations of on-premise appliances, hosted private clouds, and public cloud-native services depending on latency, data residency, and control requirements. Together, these shifts compel organizations to adopt flexible RBAC architectures that can evolve with changing business needs while maintaining strong governance and operational efficiency.
Navigating procurement friction and deployment resilience as 2025 tariff shifts prompt strategic moves toward cloud-hosted RBAC, vendor diversification, and modular architectures
The imposition of tariffs and trade policy measures in 2025 has introduced new complexities into procurement and deployment strategies for RBAC-related solutions. Hardware components used for on-premise deployments, including servers, network appliances, and secure hardware modules, have experienced procurement friction as organizations reassessed supply chains and total cost of acquisition. These developments have increased the appeal of cloud-based and hosted private cloud options, where infrastructure procurement is abstracted from the customer and supply-chain risk is mitigated through provider contracts and geographic redundancy.
In software and services, tariff-driven cost pressures have accelerated negotiations around licensing models, prompting some vendors and customers to favor subscription and consumption-based agreements that reduce upfront capital expenditure. This shift, in turn, has influenced integration timelines and vendor selection criteria, with enterprises placing a premium on vendors that provide flexible deployment options and predictable operational expense profiles.
From a strategic perspective, tariffs have also underscored the importance of supply chain transparency and vendor diversity. Organizations are increasingly incorporating vendor risk assessments into their procurement frameworks, demanding clearer visibility into component origins, firmware provenance, and third-party dependencies. Consequently, procurement teams are collaborating more closely with security and compliance stakeholders to ensure that RBAC implementations remain resilient under shifting trade conditions.
Operationally, the cumulative impact includes extended lead times for certain hardware-intensive projects, increased evaluation of hosted or public cloud RBAC offerings, and a stronger focus on modular architectures that allow for phased rollouts. These changes are reinforcing the value of architecture decisions that prioritize portability, interoperability, and the minimization of tightly coupled hardware dependencies.
Detailed segmentation-driven understanding of RBAC adoption patterns across product offerings, deployment modalities, end-user verticals, distribution channels, and enterprise size variations
Segmentation analysis reveals how RBAC adoption and implementation complexity vary across product, deployment, end-user, distribution channel, and company size dimensions, each influencing strategic choices and operational trade-offs. Based on Product Type, the landscape encompasses Hardware, Services, and Software. The Software dimension further divides into Custom Software and Packaged Software; Custom Software then differentiates into Implementation and Maintenance services, while Packaged Software is split between Horizontal Specific and Vertical Specific solutions. This product-level granularity affects decisions related to integration effort, customization needs, and long-term support obligations.
Based on Deployment Type, organizations choose between Cloud and On Premise environments. The Cloud option breaks down into Private Cloud and Public Cloud, with Private Cloud further subdivided into Hosted Private Cloud and On Site Private Cloud. These deployment distinctions shape considerations such as data residency, latency, control, and operational responsibility, prompting diverse architectural and governance approaches.
Based on End User, the RBAC landscape spans Banking, Financial Services, Healthcare, Insurance, Manufacturing, and Retail. Within Banking, segmentation occurs across Commercial Banking and Investment Banking, while Financial Services divides into Asset Management and Capital Markets. Healthcare distinguishes Clinic and Hospital settings, Insurance separates Life Insurance and Non Life Insurance, and Manufacturing differentiates Automotive and Electronics. These end-user differentiations drive sector-specific requirements for auditability, regulatory controls, and integration with vertical workflows.
Based on Distribution Channel, models include Direct Sales, Online Store, and Resellers. Resellers themselves encompass System Integrators and Value Added Resellers, which affects how implementations are scoped, who leads integration, and where post-deployment responsibilities lie. Based on Company Size, organizations range from Large Enterprise to Small Medium Enterprise, and the Small Medium Enterprise category further separates into Medium Enterprise and Small Enterprise. Company size influences procurement cycles, budget constraints, and in-house capability for ongoing administration.
Together, these segmentation vectors highlight that RBAC strategies must be tailored: product selection depends on the balance between customization and off-the-shelf speed; deployment decisions hinge on control and compliance needs; verticals impose unique operational and regulatory constraints; distribution choices determine implementation ownership; and company size governs the scale and pace of adoption. Understanding these intersecting layers is essential for designing role frameworks that are both secure and operationally sustainable.
How regional regulatory environments, cloud adoption rates, and data sovereignty concerns are shaping RBAC deployment priorities across the Americas, EMEA, and Asia-Pacific
Regional dynamics materially influence RBAC priorities, deployment choices, and vendor engagement strategies across global operations. In the Americas, organizations emphasize rapid adoption of cloud-native controls and identity federation to support distributed workforces, with a strong focus on scalable integration with public cloud providers. This region tends to prioritize operational agility and rapid time-to-deployment, while balancing regulatory expectations around data protection and breach notification. Consequently, enterprises often select vendors that provide robust APIs, mature cloud integrations, and an ecosystem of managed services.
In Europe, Middle East & Africa, regulatory complexity and data sovereignty considerations drive a heavier reliance on private cloud and on-premise deployments, particularly for highly regulated industries. Organizations across these jurisdictions frequently demand localized data controls, detailed audit trails, and contractual assurances regarding data handling. This results in procurement patterns that favor flexible deployment options and strong professional services capabilities to ensure compliance with regional frameworks.
In the Asia-Pacific region, the RBAC landscape is characterized by rapid digital modernization across both established and emerging economies. Hybrid deployment models are common as organizations modernize legacy systems while adopting public cloud for new workloads. Regional differences in infrastructure maturity and regulatory posture lead to varied vendor strategies; some organizations pursue aggressive cloud adoption for scalability and cost efficiency, while others emphasize hosted private cloud or on-site private cloud models to meet specific latency and sovereignty requirements. Across all regions, there is a shared emphasis on integrating RBAC with broader identity ecosystems to support cross-border operations and supplier chains.
Competitive differentiation driven by policy-as-code, deep integrations, professional services, and hybrid delivery models among RBAC vendors and integrators
Leading vendors and service providers in the RBAC ecosystem are differentiating through a combination of technological depth, integration breadth, and service-led delivery models. Some vendors focus on robust policy engines and policy-as-code capabilities that enable programmatic control and continuous enforcement, while others emphasize turnkey packaged solutions optimized for specific vertical workflows. In parallel, professional service organizations and system integrators have expanded their offerings to include role engineering workshops, entitlement rationalization, and operational training to accelerate adoption and reduce errors in role design.
Partnerships and ecosystem plays are prominent among established and emerging providers. Integrations with identity providers, cloud platforms, and IT service management tooling create stickiness and reduce the friction of deployment. Vendors that invest in interoperable APIs, standardized connectors, and a rich developer ecosystem are better positioned to win engagements that require complex orchestration across heterogeneous environments. At the same time, companies that offer flexible licensing models and packaged implementation templates for regulated industries are gaining traction where predictable compliance outcomes are essential.
Competitive differentiation is also shaped by investments in automation and analytics. Vendors that integrate behavior-based analytics to inform role rationalization and continuous certification processes provide tangible operational efficiencies. Meanwhile, security-conscious organizations are prioritizing providers with strong secure development lifecycles, transparent supply-chain practices, and demonstrable controls around firmware and component provenance. Overall, the supplier landscape is moving toward hybrid offerings that blend cloud services, hosted private cloud options, and on-premise appliances to meet diverse enterprise needs.
Practical, prioritized steps for executives to modernize RBAC through role engineering, policy-as-code, telemetry-driven governance, and deployment portability
For industry leaders seeking to strengthen identity governance and access controls, a set of actionable recommendations can accelerate secure adoption and measurable risk reduction. Begin by defining a clear role engineering initiative that maps business functions to access needs and prioritizes critical entitlements for immediate remediation. This should be paired with continuous certification cycles and automated reconciliation to prevent privilege creep and to preserve auditability over time.
Architect for portability by designing RBAC policies that are infrastructure-agnostic and that can be applied across on-premise, hosted private cloud, and public cloud environments. Adopt policy-as-code practices to version, test, and deploy access rules with the same rigor used for application code. Complement this with an integration-first approach that ensures your identity provider, cloud providers, and critical applications are orchestrated through standardized APIs and connectors to reduce manual interventions.
Invest in telemetry and analytics to inform role lifecycle decisions; behavioral baselining and anomaly detection can surface risky entitlements and inform targeted access reviews. Additionally, prioritize vendor agreements that offer flexible licensing and deployment options to decouple strategic control from procurement-driven constraints. Finally, embed RBAC modernization within a broader change management program to address organizational friction, clarify ownership between security and IT operations, and to train stakeholders in new governance workflows. These steps together will reduce operational overhead and increase the resilience of access controls in dynamic environments.
An evidence-driven research approach combining expert interviews, technical literature review, and scenario analyses to produce actionable insights into RBAC deployment and governance
This research synthesizes primary and secondary approaches designed to deliver both depth and practical relevance. Primary research consisted of structured interviews and guided briefings with senior security architects, identity and access management leads, procurement officers, and system integrators across diverse industries. These conversations provided qualitative insights into deployment preferences, vendor selection criteria, operational challenges, and the ways organizations are adapting governance processes to support RBAC modernization.
Secondary research involved a comprehensive review of vendor documentation, industry standards, and regulatory guidance to validate architectural patterns and compliance imperatives. Technical white papers, product briefs, and publicly available governance frameworks were analyzed to map feature capabilities and integration approaches. Where appropriate, vendor disclosures and customer case studies were used to corroborate implementation patterns and to illustrate practical deployment scenarios.
Analytical techniques included role taxonomy mapping, deployment trade-off analysis, and scenario-driven evaluation of procurement and operational decisions. Throughout the research, care was taken to triangulate findings across multiple sources to ensure robustness, and to focus on actionable insights rather than quantitative estimates. The methodology emphasizes replicability and transparency, allowing practitioners to trace recommendations back to the underlying evidence and expert inputs.
Strategic conclusion emphasizing RBAC as an ongoing capability requiring cross-functional governance, automation, and portability to meet regulatory and operational demands
In conclusion, Role-Based Access Control has evolved into a strategic control that must be architected to accommodate modern infrastructure, regulatory scrutiny, and dynamic operational models. Enterprises that prioritize role engineering, embrace automation and policy-as-code, and architect policies for portability across on-premise and cloud environments are best positioned to reduce risk while enabling business agility. The interplay between procurement considerations, regional regulatory constraints, and vendor capabilities means that RBAC programs should be tailored rather than one-size-fits-all, with particular attention paid to vertical requirements and company scale.
Moving forward, organizations that operationalize telemetry, invest in continuous certification, and maintain a disciplined approach to vendor risk assessment will achieve stronger governance outcomes. Integrating RBAC modernization with broader identity and access management strategies will deliver not only improved security posture but also measurable operational efficiencies. This conclusion underscores that RBAC is no longer a static control but a continuously managed capability that requires executive sponsorship, cross-functional collaboration, and a pragmatic roadmap to achieve sustained effectiveness.
Additional Product Information:
- Purchase of this report includes 1 year online access with quarterly updates.
- This report can be updated on request. Please contact our Customer Experience team using the Ask a Question widget on our website.
Table of Contents
7. Cumulative Impact of Artificial Intelligence 2025
16. China Role-Based Access Control Market
Companies Mentioned
The key companies profiled in this Role-Based Access Control market report include:- Amazon Web Services Inc.
- BeyondTrust Corporation
- CyberArk Software Ltd.
- ForgeRock Inc.
- IBM Corporation
- Micro Focus International plc
- Microsoft Corporation
- Okta Inc.
- One Identity LLC
- Oracle Corporation
- Ping Identity Holding Corp.
- RSA Security LLC
- SailPoint Technologies Holdings Inc.
- Salesforce Inc.
- SAP SE
- Saviynt Inc.
Table Information
| Report Attribute | Details |
|---|---|
| No. of Pages | 196 |
| Published | January 2026 |
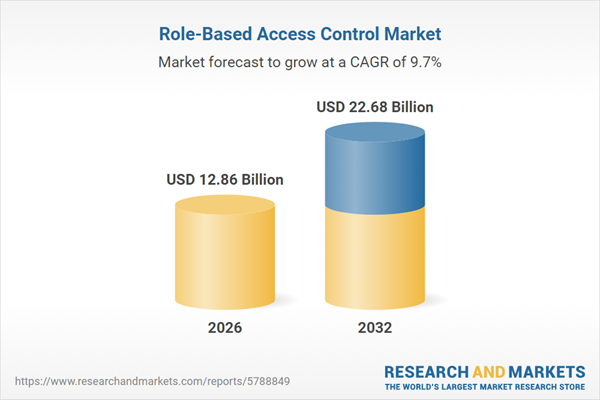
| Forecast Period | 2026 - 2032 |
| Estimated Market Value ( USD | $ 12.86 Billion |
| Forecasted Market Value ( USD | $ 22.68 Billion |
| Compound Annual Growth Rate | 9.7% |
| Regions Covered | Global |
| No. of Companies Mentioned | 17 |