The Cloud Security Market in Energy is expected to grow from USD 1.50 billion in 2025 to USD 2.41 billion by 2030, at a CAGR of 10% during the forecast period (2025-2030).
Considering that nations want to reduce their carbon impact and switch to renewable energy sources, the energy sector is in the midst of a major transformation. The need to reduce greenhouse gas emissions, the falling cost of renewables, and the adoption of new technologies, such as smart grids, have increased the demand for storing, managing, and analyzing data. Energy firms have greatly benefited from using cloud technology to collect and utilize this data. Utility companies are collaborating with various cloud computing firms to provide security for this important data.
Key Highlights
- According to Gartner, by 2024, cloud computing will account for more than 45% of IT spending on system infrastructure, infrastructure software, application software, and business process outsourcing. According to a recent Deloitte report, 83% of energy and utility companies either use cloud services or want to do so within the next two years. Many variables, such as greater agility and flexibility, lower capital expenditure (CapEx) costs, and enhanced operational efficiency, drive the use of clouds in the energy and utilities sector.
- Security becomes paramount when the systems are accessed outside the office premises. Legacy equipment is one of the main challenges of the energy sector. Operational Technology (OT) networks are becoming more connected because they are typically constructed using equipment over 15 years old. Security issues arise due to the fusion of the IT (Information Technology) and OT environments.
- The COVID-19 pandemic was the most important time for Cloud Storage as a revolutionary technology, further driving the demand for cloud security services. For power plants accessing the systems securely from remote locations became essential. Some companies switched to digital solutions like Zero Trust architecture, which provided security teams with greater contextual information by combining feeds from various places on a single dashboard in real time.
- April 2022 - Bharat Petroleum Corporation (BPCL) signed a contract with Microsoft that will give BPCL the intelligence to revamp its operations, create smarter supply chains, and boost customer engagement. Microsoft will provide network and security services to the organization in this seven year deal.
Energy Sector Cloud Security Market Trends
Increasing Number of Cyber Attacks to Drive the Need for Cloud Security in the Energy Sector
- Companies in the energy sector frequently have to manage thousands of different suppliers, operate in many locations, and source their products from other continents. This makes them a prominent target for both hackers and cyber terrorists. To ensure the appropriate level of security, companies must monitor the vulnerabilities in their products during their entire lifecycle and adhere to the most recent standards and regulations.
- A cyber attack can cost a lot of money and lead to power disruptions or the leaking of confidential customer data. This could significantly affect the company's business operations and those who depend on its services. By hiring a cybersecurity company, Energy firms can encrypt sensitive data and train employees on how to protect from malicious attacks.
- In february 2022, the disruption at Oiltanking in Germany, SEA-Invest in Belgium, and Evos in the Netherlands affected dozens of terminals with oil storage and transport worldwide. These cyber-attacks compel companies to operate at a limited capacity, giving rise to supply chain issues.
- Further, in April 2022 - Oil India suffered a cyberattack disrupting its operations in Assam. The cyberattack occurred at one of the workstations of OIL's Geological and Reservoir department (Oil India Ltd.). The cyberattacker demanded USD 7.5 million as a ransom through a note from the infected PC. However, the drilling and production work was unaffected.
- Moreover, in November 2023, Nasuni, one of the leading hybrid cloud storage solutions, announced a strategic partnership with Cegal, one of the global leaders of digital solutions for the energy industry. Energy Organizations Increasingly Rely on Nasuni for Accelerating Cloud Transformations, Modernizing File Data Architectures and Enhanced Cyber Resiliency Nasuni and Cegal are assisting organizations to accelerate their cloud transformations by providing the technology infrastructure and expertise needed to manage and protect data at scale from any location.
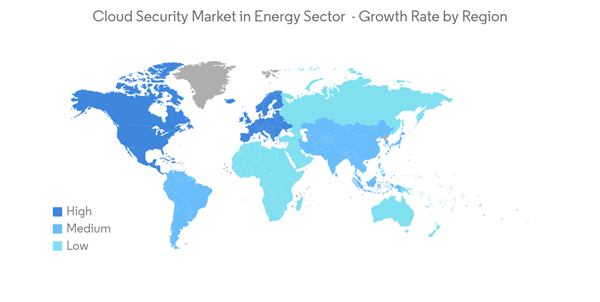
Europe is Expected to Witness the Highest Growth
- Public agencies and the European government had to adapt their organizations to meet the increased demand for online services. This created a demand for cloud computing technologies that led infrastructure and services essential for staying competitive in a hypercomplex global economy.
- The European energy system needs to undergo a significant transition, with digitalization playing a pivotal role, in addressing the climate issue and reduce the EU's reliance on Russian fossil fuels. To support these developments, European Union formed a Smart Energy Expert Group to support the development and rolling out of a common European data space for energy.
- 51% of all EU households and SMEs are equipped with smart electricity meters, and various policies have been introduced to guide the digitalization of energy as issues like security, privacy, and consumer protection. In consultation with Network and Information Security Group (NIS), the Commission will identify the specific ICT services, systems, and products that might be subjected to coordinated risk assessments with priority.
- The UK experienced the warmest summer in 2022, and the extreme weather caused temporary failures at Oracle and Google Cloud's data centers in London. Water scarcity and energy insecurity made data center operators uneasy, which affected cloud computing operations. To overcome these uncertainties, EC plans an investment of USD 620 billion in the electricity grid, including USD 180.4 billion in digitalization.
Energy Sector Cloud Security Industry Overview
There is intense competition with several providers of Cloud Security. The major players include IBM Corporation, Intel Security- McAfee, Symantec Corporation, Cisco Systems, Inc., CA Technologies, CA Technologies, Nutanix, Netskope, Inc., and ProtectWise. Due to high competency, the market concentration will be low.
- Microsoft and Schlumberger launched Microsoft Energy Data Services. This data solution will make it possible for energy corporations to create software applications quickly, and it will be powered by Microsoft's secure and trusted cloud services.
- Schlumberger and Cognite announced a strategic partnership. Cognite provides software and IoT services to industrial companies. While integrating data from reservoirs, wells, and facilities into a single, open platform, clients can utilize embedded AI and advanced analytics capabilities to maximize production, save costs, and minimize operational footprint. Schlumberger will provide customers with access to the Enterprise Data Solution.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
This product will be delivered within 2 business days.
Table of Contents
Companies Mentioned (Partial List)
A selection of companies mentioned in this report includes, but is not limited to:
- IBM Corporation
- Intel Security - McAfee
- Cisco Systems, Inc.
- Broadcom Inc.
- Qualys, Inc.
- Nutanix
- ProtectWise
- AmazonWebServices