Global Counter Cyber Terrorism Market - Key Trends and Drivers Summarized
From Bombs to Bytes: Why Terrorists Are Trading Guns for Keyboards
Terrorists are increasingly going digital, recognizing the cyber realm as a potent battleground that extends their reach and enhances their anonymity. By leveraging digital technologies, they can orchestrate attacks remotely, targeting critical infrastructure, financial systems, and public information networks without physically crossing borders. The internet also serves as a powerful tool for propaganda, allowing terrorist groups to spread their ideologies, recruit new members, and incite fear far beyond their immediate geographical locations. Additionally, the digital shift comes with lower risks of detection and the ability to cause significant disruptions with minimal physical resources. In an interconnected world, the cyber approach not only broadens the scope of potential targets but also complicates the task for counterterrorism agencies, making digital fluency an essential weapon in the modern terrorist arsenal.Defending the Digital Front: How Crucial Is Counter Cyber Terrorism Today?
In an era where digital technology permeates every facet of our lives, the threat of cyber terrorism has emerged as a critical security challenge. Cyber terrorists exploit the internet, computer systems, and network vulnerabilities to conduct attacks that can significantly disrupt the functionality of national infrastructures, such as power grids, financial systems, and healthcare records. Counter cyber terrorism efforts are thus vital in identifying, responding to, and mitigating threats that could have catastrophic consequences. These efforts encompass a range of strategies, from deploying sophisticated cybersecurity technologies to implementing comprehensive legal frameworks and cooperation between international intelligence communities to combat these digital threats effectively.What Technologies Are Pioneering the Fight Against Cyber Terrorism?
Advancements in technology are on the front lines in the battle against cyber terrorism. Artificial Intelligence (AI) and Machine Learning (ML) are being increasingly harnessed to predict and analyze cyber threats before they manifest into attacks. These technologies can identify patterns and anomalies that suggest potential cyber terrorist activities, allowing security systems to adapt and respond more effectively. Blockchain technology is also becoming a crucial tool in this field, offering enhanced security features such as decentralized data management and cryptographic protection, which are instrumental in safeguarding sensitive information from unauthorized access and tampering. Furthermore, quantum computing presents a future avenue for potentially revolutionizing cyber defense by enhancing encryption methods and developing new standards in cybersecurity protocols.Are There Challenges in Implementing Effective Counter Cyber Terrorism Measures?
While the development and implementation of advanced technologies are critical in fighting cyber terrorism, several challenges hinder these efforts. One of the primary issues is the pace of technological change, which often outstrips the speed of security development, leaving systems vulnerable to new types of cyber attacks. There is also the complexity of cyber terrorist networks, which operate across multiple jurisdictions, making it difficult to track and neutralize threats without extensive international cooperation. Furthermore, there is a constant shortage of skilled cybersecurity professionals who can manage and counteract sophisticated cyber threats. These challenges require ongoing commitment and innovation from governments, private sectors, and educational institutions to keep up with the dynamic nature of cyber terrorism.What Factors Are Fueling the Expansion of the Counter Cyber Terrorism Market?
The growth in the counter cyber terrorism market is driven by several factors, reflecting the increasing complexity and frequency of cyber attacks. As more critical infrastructures and personal data migrate online, the stakes in protecting these digital assets are higher than ever. The escalating sophistication of cyber terrorists compels continuous advancements in cybersecurity technology and strategies. Economic expansion and the digital transformation of businesses globally are also contributing to the surge in demand for robust cybersecurity measures. Additionally, regulatory requirements and data protection laws in various countries mandate stringent cybersecurity protocols, propelling investment and development in the sector. Moreover, the growing public awareness of cyber threats is encouraging organizations to prioritize their digital defenses, further driving market growth. These combined forces ensure that counter cyber terrorism remains a key focus in the quest to secure our digital future.Report Scope
The report analyzes the Counter Cyber Terrorism market, presented in terms of market value (US$). The analysis covers the key segments and geographic regions outlined below:- Segments: Type (Firewall, Web Mining & Intelligence, Counter Cyber Terrorism Personnel, CT-SNAIR, Cryptography Techniques, Other Types).
- Geographic Regions/Countries: World; United States; Canada; Japan; China; Europe (France; Germany; Italy; United Kingdom; and Rest of Europe); Asia-Pacific; Rest of World.
Key Insights:
- Market Growth: Understand the significant growth trajectory of the Network Security Solution segment, which is expected to reach US$12.4 Billion by 2032 with a CAGR of 5.3%. The Endpoint Security Solution segment is also set to grow at 3.0% CAGR over the analysis period.
- Regional Analysis: Gain insights into the U.S. market, valued at $9.5 Billion in 2025, and China, forecasted to grow at an impressive 4.2% CAGR to reach $7.8 Billion by 2032. Discover growth trends in other key regions, including Japan, Canada, Germany, and the Asia-Pacific.
Why You Should Buy This Report:
- Detailed Market Analysis: Access a thorough analysis of the Global Counter Cyber Terrorism Market, covering all major geographic regions and market segments.
- Competitive Insights: Get an overview of the competitive landscape, including the market presence of major players across different geographies.
- Future Trends and Drivers: Understand the key trends and drivers shaping the future of the Global Counter Cyber Terrorism Market.
- Actionable Insights: Benefit from actionable insights that can help you identify new revenue opportunities and make strategic business decisions.
Key Questions Answered:
- How is the Global Counter Cyber Terrorism Market expected to evolve by 2032?
- What are the main drivers and restraints affecting the market?
- Which market segments will grow the most over the forecast period?
- How will market shares for different regions and segments change by 2032?
- Who are the leading players in the market, and what are their prospects?
Report Features:
- Comprehensive Market Data: Independent analysis of annual sales and market forecasts in US$ Million from 2025 to 2032.
- In-Depth Regional Analysis: Detailed insights into key markets, including the U.S., China, Japan, Canada, Europe, Asia-Pacific, Latin America, Middle East, and Africa.
- Company Profiles: Coverage of players such as Boeing Co., The, Booz Allen Hamilton, Inc., Cisco Systems, Inc., Computer Science Corporation and more.
- Complimentary Updates: Receive free report updates for one year to keep you informed of the latest market developments.
Some of the companies featured in this Counter Cyber Terrorism market report include:
- Boeing Co.
- The
- Booz Allen Hamilton, Inc.
- Cisco Systems, Inc.
- Computer Science Corporation
- General Dynamics Corporation
- IBM Corporation
- Intel Corporation
- Leidos Holdings, Inc.
- Leonardo SpA
- Lockheed Martin Corporation
- Northrop Grumman Corporation
- Palo Alto Networks, Inc.
- SAP SE
- Thales Group
Domain Expert Insights
This market report incorporates insights from domain experts across enterprise, industry, academia, and government sectors. These insights are consolidated from multilingual multimedia sources, including text, voice, and image-based content, to provide comprehensive market intelligence and strategic perspectives. As part of this research study, the publisher tracks and analyzes insights from 5,415 domain experts. Clients may request access to the network of experts monitored for this report, along with the online expert insights tracker.Table of Contents
Companies Mentioned (Partial List)
A selection of companies mentioned in this report includes, but is not limited to:
- Boeing Co.
- The
- Booz Allen Hamilton, Inc.
- Cisco Systems, Inc.
- Computer Science Corporation
- General Dynamics Corporation
- IBM Corporation
- Intel Corporation
- Leidos Holdings, Inc.
- Leonardo SpA
- Lockheed Martin Corporation
- Northrop Grumman Corporation
- Palo Alto Networks, Inc.
- SAP SE
- Thales Group
Table Information
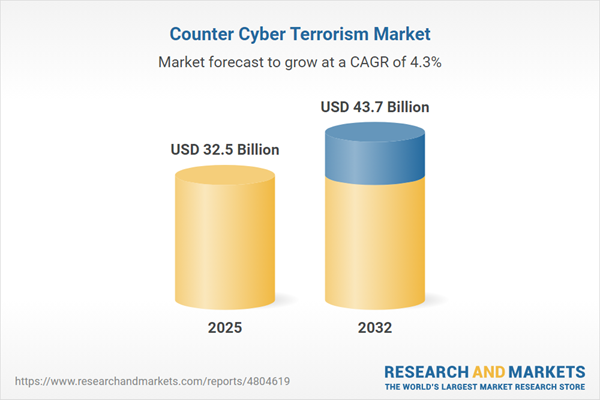
| Report Attribute | Details |
|---|---|
| No. of Pages | 418 |
| Published | May 2026 |
| Forecast Period | 2025 - 2032 |
| Estimated Market Value ( USD | $ 32.5 Billion |
| Forecasted Market Value ( USD | $ 43.7 Billion |
| Compound Annual Growth Rate | 4.3% |
| Regions Covered | Global |