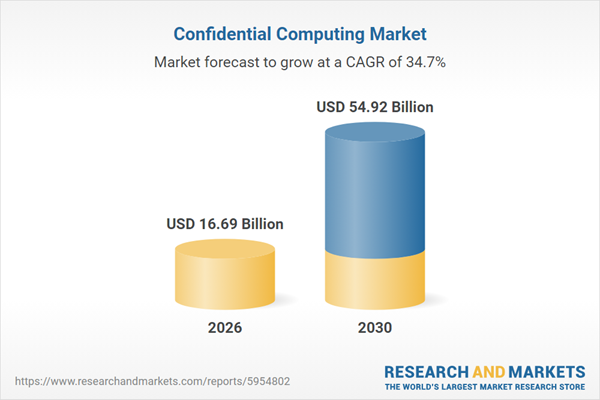
The confidential computing market size is expected to see exponential growth in the next few years. It will grow to $54.92 billion in 2030 at a compound annual growth rate (CAGR) of 34.7%. The growth in the forecast period can be attributed to expansion of confidential computing in healthcare and government, integration with AI and big data analytics, increased multi-cloud deployments, adoption by fintech and digital finance sectors, regulatory push for enhanced data privacy. Major trends in the forecast period include hardware-based trusted execution environments (tees), confidential virtual machines and containers, advanced encryption and privacy-enhancing software, managed and integration services for confidential computing, secure data processing across multi-cloud environments.
The increasing cyber intrusion activities are anticipated to drive the growth of the confidential computing market in the coming years. Cyber intrusion activities involve unauthorized actions or breaches conducted by individuals, groups, or entities to gain access to computer systems, networks, or data without permission. With greater connectivity, more sophisticated attack methods, and limited cybersecurity awareness and preparedness, incidents of cyber intrusions are on the rise. Confidential computing plays a key role in combating these intrusions by safeguarding sensitive data from unauthorized access or manipulation and enhancing the security of computing environments. For example, in July 2024, Check Point Software Technologies Ltd., an Israel-based cybersecurity firm, reported that cyberattacks on corporate networks increased by 30% in weekly attacks during the second quarter of 2024 compared to the same period in 2023, and rose by 25% from the first quarter of 2024. Consequently, the surge in cyber intrusion activities is propelling the growth of the confidential computing market.
Major companies in the confidential computing market are focusing on creating advanced solutions such as attestation-enforced container platforms to improve data security and operational scalability. Attestation-enforced container platforms are container environments that validate the integrity, authenticity, and security of container images before deployment using cryptographic attestation mechanisms. For instance, in July 2025, QLAD, a US-based company, introduced its Kubernetes-native confidential computing platform featuring Armored Containers and workload-level trusted execution. The platform streamlines confidential computing adoption with single-command deployment, integrates seamlessly with existing Kubernetes infrastructure, and protects sensitive workloads without requiring code modifications or specialized expertise. It offers execution-level protection for data in use, along with optional persistent encryption for data at rest and in transit. Additionally, it uses pod-level cryptographic attestation to establish verifiable trust across environments and supports vendor-neutral deployment across multi-cloud, hybrid, and edge infrastructures.
In May 2025, Arcium, a Switzerland-based provider of a decentralized confidential computing network and encrypted computation frameworks, acquired Inpher Inc. for an undisclosed amount. Through this acquisition, Arcium aims to accelerate its mainnet launch and expand its offerings in privacy-preserving AI and encrypted machine-learning workloads. Inpher Inc., a US-based confidential computing company, specializes in privacy-preserving data computation and secure multi-party computation.
Major companies operating in the confidential computing market are Google LLC; Microsoft Corporation; Alibaba Group Holding Limited; Huawei Technologies Co. Ltd; Amazon Web Services Inc; Intel Corporation; International Business Machines Corporation; Cisco Systems Inc.; Oracle Corporation; Telefónica Group; Advanced Micro Devices Inc; Capgemini SE; Thales Group; Vmware Inc.; Swisscom AG; Wipro Limited; Arm Holdings; OVH Groupe SA; Cyxtera Technologies; HUB Security Ltd.; Applied Blockchain Ltd.; PhoenixNAP; Fortanix Inc.; Anjuna Security Inc.; dq technologies AG; Opaque Systems Inc; R3 Inc.; Cysec SA.
North America was the largest region in the confidential computing market in 2025. Asia-Pacific is expected to be the fastest-growing region in the forecast period. The regions covered in the confidential computing market report are Asia-Pacific, South East Asia, Western Europe, Eastern Europe, North America, South America, Middle East, Africa. The countries covered in the confidential computing market report are Australia, Brazil, China, France, Germany, India, Indonesia, Japan, Taiwan, Russia, South Korea, UK, USA, Canada, Italy, Spain.
Tariffs have impacted the confidential computing market by raising the cost of imported specialized hardware, including trusted execution environments, secure processors, and hardware security modules, as well as encryption software tools. The segments most affected include hardware components and software solutions, particularly in regions such as North America, Europe, and Asia-Pacific, which rely heavily on imported technology. While tariffs have increased operational costs, they have also encouraged local manufacturing and innovation, prompting providers to optimize solutions and explore domestic alternatives for confidential computing deployments.
The confidential computing market research report is one of a series of new reports that provides confidential computing market statistics, including confidential computing industry global market size, regional shares, competitors with a confidential computing market share, detailed confidential computing market segments, market trends and opportunities, and any further data you may need to thrive in the confidential computing industry. This confidential computing market research report delivers a complete perspective of everything you need, with an in-depth analysis of the current and future scenario of the industry.
Confidential computing encompasses technologies and practices aimed at safeguarding sensitive data and processes within computing environments, ensuring their confidentiality and security, particularly during processing or analysis by cloud or other computing services.
The primary components of confidential computing include hardware, software, and services. Hardware components constitute physical elements within computer systems designed for specific functions. They encompass various deployments such as on-premises and cloud setups, serving diverse applications such as data security, secure enclaves, and user transparency. These components find applications across various industry verticals including banking, financial services and insurance (BFSI), government and defense, healthcare, information technology (IT) and telecommunications, retail, manufacturing, and others.
The confidential computing market consists of revenues earned by entities by providing services such as managed services, secure enclave provisioning, encrypted data processing, key management, security audits and consulting, compliance and regulatory support, and integration and customization services. The market value includes the value of related goods sold by the service provider or included within the service offering. The confidential computing market also includes sales of hardware firewalls, intrusion detection and prevention systems (IDPS), secure enclave processors, hardware security modules, trusted platform modules, and secure storage devices. Values in this market are ‘factory gate’ values, that is, the value of goods sold by the manufacturers or creators of the goods, whether to other entities (including downstream manufacturers, wholesalers, distributors, and retailers) or directly to end customers. The value of goods in this market includes related services sold by the creators of the goods.
The market value is defined as the revenues that enterprises gain from the sale of goods and/or services within the specified market and geography through sales, grants, or donations in terms of the currency (in USD unless otherwise specified).
The revenues for a specified geography are consumption values that are revenues generated by organizations in the specified geography within the market, irrespective of where they are produced. It does not include revenues from resales along the supply chain, either further along the supply chain or as part of other products.
This product will be delivered within 1-3 business days.
Table of Contents
Executive Summary
Confidential Computing Market Global Report 2026 provides strategists, marketers and senior management with the critical information they need to assess the market.This report focuses confidential computing market which is experiencing strong growth. The report gives a guide to the trends which will be shaping the market over the next ten years and beyond.
Reasons to Purchase:
- Gain a truly global perspective with the most comprehensive report available on this market covering 16 geographies.
- Assess the impact of key macro factors such as geopolitical conflicts, trade policies and tariffs, inflation and interest rate fluctuations, and evolving regulatory landscapes.
- Create regional and country strategies on the basis of local data and analysis.
- Identify growth segments for investment.
- Outperform competitors using forecast data and the drivers and trends shaping the market.
- Understand customers based on end user analysis.
- Benchmark performance against key competitors based on market share, innovation, and brand strength.
- Evaluate the total addressable market (TAM) and market attractiveness scoring to measure market potential.
- Suitable for supporting your internal and external presentations with reliable high-quality data and analysis
- Report will be updated with the latest data and delivered to you along with an Excel data sheet for easy data extraction and analysis.
- All data from the report will also be delivered in an excel dashboard format.
Description
Where is the largest and fastest growing market for confidential computing? How does the market relate to the overall economy, demography and other similar markets? What forces will shape the market going forward, including technological disruption, regulatory shifts, and changing consumer preferences? The confidential computing market global report answers all these questions and many more.The report covers market characteristics, size and growth, segmentation, regional and country breakdowns, total addressable market (TAM), market attractiveness score (MAS), competitive landscape, market shares, company scoring matrix, trends and strategies for this market. It traces the market’s historic and forecast market growth by geography.
- The market characteristics section of the report defines and explains the market. This section also examines key products and services offered in the market, evaluates brand-level differentiation, compares product features, and highlights major innovation and product development trends.
- The supply chain analysis section provides an overview of the entire value chain, including key raw materials, resources, and supplier analysis. It also provides a list competitor at each level of the supply chain.
- The updated trends and strategies section analyses the shape of the market as it evolves and highlights emerging technology trends such as digital transformation, automation, sustainability initiatives, and AI-driven innovation. It suggests how companies can leverage these advancements to strengthen their market position and achieve competitive differentiation.
- The regulatory and investment landscape section provides an overview of the key regulatory frameworks, regularity bodies, associations, and government policies influencing the market. It also examines major investment flows, incentives, and funding trends shaping industry growth and innovation.
- The market size section gives the market size ($b) covering both the historic growth of the market, and forecasting its development.
- The forecasts are made after considering the major factors currently impacting the market. These include the technological advancements such as AI and automation, Russia-Ukraine war, trade tariffs (government-imposed import/export duties), elevated inflation and interest rates.
- The total addressable market (TAM) analysis section defines and estimates the market potential compares it with the current market size, and provides strategic insights and growth opportunities based on this evaluation.
- The market attractiveness scoring section evaluates the market based on a quantitative scoring framework that considers growth potential, competitive dynamics, strategic fit, and risk profile. It also provides interpretive insights and strategic implications for decision-makers.
- Market segmentations break down the market into sub markets.
- The regional and country breakdowns section gives an analysis of the market in each geography and the size of the market by geography and compares their historic and forecast growth.
- Expanded geographical coverage includes Taiwan and Southeast Asia, reflecting recent supply chain realignments and manufacturing shifts in the region. This section analyzes how these markets are becoming increasingly important hubs in the global value chain.
- The competitive landscape chapter gives a description of the competitive nature of the market, market shares, and a description of the leading companies. Key financial deals which have shaped the market in recent years are identified.
- The company scoring matrix section evaluates and ranks leading companies based on a multi-parameter framework that includes market share or revenues, product innovation, and brand recognition.
Report Scope
Markets Covered:
1) By Component: Hardware; Software; Service2) By Deployment Model: On-Premises; Cloud
3) By Application: Data Security; Secure Enclaves; Pellucidity Between Users; Other Applications
4) By Industry Vertical: Banking Financial Services And Insurance (BFSI); Government And Defense; Healthcare; Information Technology (IT) And Telecommunications; Retail; Manufacturing; Other Industry Verticals
Subsegments:
1) By Hardware: Trusted Execution Environments (TEEs); Hardware Security Modules (HSMs); Secure Processors; Trusted Platform Modules (TPMs)2) By Software: Confidential Virtual Machines (VMs); Confidential Containers; Security And Privacy-Enhancing Software; Encryption Software
3) By Service: Managed Services; Consulting Services; Integration And Deployment Services; Support And Maintenance Services
Companies Mentioned: Google LLC; Microsoft Corporation; Alibaba Group Holding Limited; Huawei Technologies Co. Ltd; Amazon Web Services Inc; Intel Corporation; International Business Machines Corporation; Cisco Systems Inc.; Oracle Corporation; Telefónica Group; Advanced Micro Devices Inc; Capgemini SE; Thales Group; Vmware Inc.; Swisscom AG; Wipro Limited; Arm Holdings; OVH Groupe SA; Cyxtera Technologies; HUB Security Ltd.; Applied Blockchain Ltd.; PhoenixNAP; Fortanix Inc.; Anjuna Security Inc.; dq technologies AG; Opaque Systems Inc; R3 Inc.; Cysec SA
Countries: Australia; Brazil; China; France; Germany; India; Indonesia; Japan; Taiwan; Russia; South Korea; UK; USA; Canada; Italy; Spain
Regions: Asia-Pacific; South East Asia; Western Europe; Eastern Europe; North America; South America; Middle East; Africa
Time Series: Five years historic and ten years forecast.
Data: Ratios of market size and growth to related markets, GDP proportions, expenditure per capita.
Data Segmentation: Country and regional historic and forecast data, market share of competitors, market segments.
Sourcing and Referencing: Data and analysis throughout the report is sourced using end notes.
Delivery Format: Word, PDF or Interactive Report + Excel Dashboard
Added Benefits:
- Bi-Annual Data Update
- Customisation
- Expert Consultant Support
Companies Mentioned
The companies featured in this Confidential Computing market report include:- Google LLC
- Microsoft Corporation
- Alibaba Group Holding Limited
- Huawei Technologies Co. Ltd
- Amazon Web Services Inc
- Intel Corporation
- International Business Machines Corporation
- Cisco Systems Inc.
- Oracle Corporation
- Telefónica Group
- Advanced Micro Devices Inc
- Capgemini SE
- Thales Group
- Vmware Inc.
- Swisscom AG
- Wipro Limited
- Arm Holdings
- OVH Groupe SA
- Cyxtera Technologies
- HUB Security Ltd.
- Applied Blockchain Ltd.
- PhoenixNAP
- Fortanix Inc.
- Anjuna Security Inc.
- dq technologies AG
- Opaque Systems Inc
- R3 Inc.
- Cysec SA
Table Information
| Report Attribute | Details |
|---|---|
| No. of Pages | 250 |
| Published | February 2026 |
| Forecast Period | 2026 - 2030 |
| Estimated Market Value ( USD | $ 16.69 Billion |
| Forecasted Market Value ( USD | $ 54.92 Billion |
| Compound Annual Growth Rate | 34.7% |
| Regions Covered | Global |
| No. of Companies Mentioned | 29 |