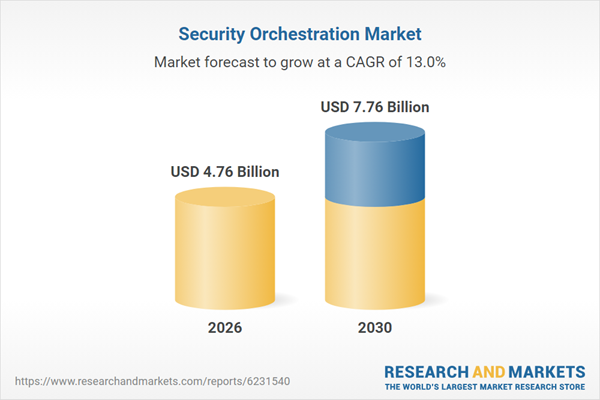
The security orchestration market size is expected to see rapid growth in the next few years. It will grow to $7.76 billion in 2030 at a compound annual growth rate (CAGR) of 13%. The growth in the forecast period can be attributed to growth of cloud native security operations, increasing adoption of artificial intelligence based threat detection, expansion of remote and hybrid work environments, rising investment in zero trust architectures, growth in cross industry cybersecurity partnerships. Major trends in the forecast period include rising adoption of automated security workflow platforms, growing demand for centralized incident management solutions, expansion of integrated threat intelligence and alert correlation tools, increasing focus on real time security analytics and monitoring, strengthening emphasis on compliance driven security operations.
The increasing frequency of cybersecurity threats is expected to propel the growth of the security orchestration market going forward. Increasing frequency of cybersecurity threats refers to the rising number of cyberattacks occurring more often over time. This frequency is increasing as malicious actors conduct more frequent and sophisticated attacks due to expanding digital adoption and evolving threat capabilities. Security orchestration supports this driver by enabling automated and coordinated threat response across security tools and workflows, allowing organizations to manage escalating attack volumes efficiently. For instance, in October 2025, according to the National Cyber Security Centre, a UK-based government body, the number of “nationally significant” cyber incidents handled between September 2024 and August 2025 more than doubled to 204 from 89 in the previous year, indicating a sharp year-on-year increase in high-impact cybersecurity threats. Therefore, the increasing frequency of cybersecurity threats is driving the growth of the security orchestration market.
Leading companies operating in the security orchestration market are focusing on developing AI-driven application security orchestration platforms to improve threat visibility, automate security workflows, and accelerate vulnerability remediation across complex development and IT environments. AI-driven security orchestration refers to the use of machine learning and data correlation algorithms to automatically discover security tools, aggregate and analyze security findings, eliminate duplicate alerts, prioritize risks based on impact, and orchestrate remediation actions across multiple security systems from a centralized platform. For example, in April 2023, Cycode, a United States-based application security company, launched Cycode Application Security Orchestration and Correlation, now known as Application Security Posture Management. The launch leverages artificial intelligence to automatically discover security tools across the software development lifecycle and correlate data from multiple application security solutions into a single view. It reduces alert fatigue by deduplicating vulnerabilities and prioritizing risks based on severity and exploitability. The platform enables security teams to respond faster to critical threats while improving overall security posture and operational efficiency.
In October 2023, Arctic Wolf Networks Inc., a US-based cybersecurity company, acquired Revelstoke for an undisclosed amount. Through this acquisition, Arctic Wolf Networks Inc. aims to incorporate Revelstoke’s Security Orchestration, Automation, and Response (SOAR) capabilities into its security operations platform to strengthen automated threat detection, incident response, and orchestration workflows, thereby enhancing its overall managed and automated security service offerings. Revelstoke is a US-based company specializing in security orchestration and automation solutions.
Major companies operating in the security orchestration market are International Business Machine Corporation, Palo Alto Networks Inc., Fortinet Inc., Rapid7 Inc., RSA Security LLC, Exabeam Inc., Securonix Inc., LogPoint A/S, Anomali Inc., Swimlane, Cyware Labs Inc., Cyberbit Ltd., Phantom Cyber, ThreatConnect Inc., Fireeye, LogRhythm Inc., Splunk Inc., DFLabs SpA, Siemplify Ltd., Cybersponse Inc.
Tariffs have influenced the security orchestration market by raising the cost of imported cybersecurity hardware appliances, network infrastructure components, and specialized monitoring equipment, which has increased deployment expenses for enterprises and managed security providers. The impact is most visible in on premises and hybrid deployments and in regions dependent on international technology imports such as parts of Asia-Pacific and Europe. However, tariffs are also encouraging the shift toward cloud based orchestration platforms, domestic software development, and localized security infrastructure investments, which can strengthen regional cybersecurity ecosystems and accelerate innovation in software centric security automation solutions.
Security orchestration refers to the process of integrating and automating multiple cybersecurity tools and workflows to improve threat detection, response, and overall security operations. It combines data from various security systems, streamlines incident management, and enables faster, coordinated responses to potential threats. It enhances efficiency and reduces the complexity of managing cybersecurity environments by centralizing monitoring, alerts, and automated actions.
The primary types of security orchestration include software and services. Software refers to platforms that automate and streamline security operations by integrating multiple tools, workflows, and processes to efficiently detect, respond to, and manage threats. These solutions are deployed through on-premises, cloud-based, and hybrid models. They are designed for organizations of different sizes, including large enterprises and small and medium enterprises, and are applied across applications such as threat detection and response, incident management, vulnerability management, compliance and audit management, and security analytics and reporting. They support end-user industries including banking, financial services, and insurance, information technology and telecommunication, government and defence, electronic commerce, and other end-user industries.
The security orchestration market includes revenues earned by entities through security workflow automation, alert triage and case management, system integration, consulting, training, and ongoing monitoring and support. The market value includes the value of related goods sold by the service provider or included within the service offering. Only goods and services traded between entities or sold to end consumers are included.
The market value is defined as the revenues that enterprises gain from the sale of goods and/or services within the specified market and geography through sales, grants, or donations in terms of the currency (in USD unless otherwise specified).
The revenues for a specified geography are consumption values that are revenues generated by organizations in the specified geography within the market, irrespective of where they are produced. It does not include revenues from resales along the supply chain, either further along the supply chain or as part of other products.
The security orchestration market research report is one of a series of new reports that provides security orchestration market statistics, including security orchestration industry global market size, regional shares, competitors with a security orchestration market share, detailed security orchestration market segments, market trends and opportunities, and any further data you may need to thrive in the security orchestration industry. This security orchestration market research report delivers a complete perspective of everything you need, with an in-depth analysis of the current and future scenario of the industry.
This product will be delivered within 1-3 business days.
Table of Contents
Executive Summary
Security Orchestration Market Global Report 2026 provides strategists, marketers and senior management with the critical information they need to assess the market.This report focuses security orchestration market which is experiencing strong growth. The report gives a guide to the trends which will be shaping the market over the next ten years and beyond.
Reasons to Purchase:
- Gain a truly global perspective with the most comprehensive report available on this market covering 16 geographies.
- Assess the impact of key macro factors such as geopolitical conflicts, trade policies and tariffs, inflation and interest rate fluctuations, and evolving regulatory landscapes.
- Create regional and country strategies on the basis of local data and analysis.
- Identify growth segments for investment.
- Outperform competitors using forecast data and the drivers and trends shaping the market.
- Understand customers based on end user analysis.
- Benchmark performance against key competitors based on market share, innovation, and brand strength.
- Evaluate the total addressable market (TAM) and market attractiveness scoring to measure market potential.
- Suitable for supporting your internal and external presentations with reliable high-quality data and analysis
- Report will be updated with the latest data and delivered to you along with an Excel data sheet for easy data extraction and analysis.
- All data from the report will also be delivered in an excel dashboard format.
Description
Where is the largest and fastest growing market for security orchestration? How does the market relate to the overall economy, demography and other similar markets? What forces will shape the market going forward, including technological disruption, regulatory shifts, and changing consumer preferences? The security orchestration market global report answers all these questions and many more.The report covers market characteristics, size and growth, segmentation, regional and country breakdowns, total addressable market (TAM), market attractiveness score (MAS), competitive landscape, market shares, company scoring matrix, trends and strategies for this market. It traces the market’s historic and forecast market growth by geography.
- The market characteristics section of the report defines and explains the market. This section also examines key products and services offered in the market, evaluates brand-level differentiation, compares product features, and highlights major innovation and product development trends.
- The supply chain analysis section provides an overview of the entire value chain, including key raw materials, resources, and supplier analysis. It also provides a list competitor at each level of the supply chain.
- The updated trends and strategies section analyses the shape of the market as it evolves and highlights emerging technology trends such as digital transformation, automation, sustainability initiatives, and AI-driven innovation. It suggests how companies can leverage these advancements to strengthen their market position and achieve competitive differentiation.
- The regulatory and investment landscape section provides an overview of the key regulatory frameworks, regularity bodies, associations, and government policies influencing the market. It also examines major investment flows, incentives, and funding trends shaping industry growth and innovation.
- The market size section gives the market size ($b) covering both the historic growth of the market, and forecasting its development.
- The forecasts are made after considering the major factors currently impacting the market. These include the technological advancements such as AI and automation, Russia-Ukraine war, trade tariffs (government-imposed import/export duties), elevated inflation and interest rates.
- The total addressable market (TAM) analysis section defines and estimates the market potential compares it with the current market size, and provides strategic insights and growth opportunities based on this evaluation.
- The market attractiveness scoring section evaluates the market based on a quantitative scoring framework that considers growth potential, competitive dynamics, strategic fit, and risk profile. It also provides interpretive insights and strategic implications for decision-makers.
- Market segmentations break down the market into sub markets.
- The regional and country breakdowns section gives an analysis of the market in each geography and the size of the market by geography and compares their historic and forecast growth.
- Expanded geographical coverage includes Taiwan and Southeast Asia, reflecting recent supply chain realignments and manufacturing shifts in the region. This section analyzes how these markets are becoming increasingly important hubs in the global value chain.
- The competitive landscape chapter gives a description of the competitive nature of the market, market shares, and a description of the leading companies. Key financial deals which have shaped the market in recent years are identified.
- The company scoring matrix section evaluates and ranks leading companies based on a multi-parameter framework that includes market share or revenues, product innovation, and brand recognition.
Report Scope
Markets Covered:
1) By Type: Software; Services2) By Deployment: On-Premises; Cloud-Based; Hybrid
3) By Organization Size: Large Enterprises; Small and Medium Enterprises
4) By Application: Threat Detection and Response; Incident Management; Vulnerability Management; Compliance and Audit Management; Security Analytics and Reporting
5) By End-User Industry: Banking, Financial Services, and Insurance (BFSI); Information Technology (IT) and Telecommunication; Government and Defence; Electronic Commerce (E-Commerce); Other End-User Industries
Subsegments:
1) By Software: Threat Detection Software; Incident Response Software; Vulnerability Management Software; Compliance Management Software; Security Analytics Software2) By Services: Consulting Services; Integration Services; Managed Security Services; Professional Services; Support and Maintenance Services
Companies Mentioned: International Business Machine Corporation; Palo Alto Networks Inc.; Fortinet Inc.; Rapid7 Inc.; RSA Security LLC; Exabeam Inc.; Securonix Inc.; LogPoint A/S; Anomali Inc.; Swimlane; Cyware Labs Inc.; Cyberbit Ltd.; Phantom Cyber; ThreatConnect Inc.; Fireeye; LogRhythm Inc.; Splunk Inc.; DFLabs SpA; Siemplify Ltd.; Cybersponse Inc.
Countries: Australia; Brazil; China; France; Germany; India; Indonesia; Japan; Taiwan; Russia; South Korea; UK; USA; Canada; Italy; Spain
Regions: Asia-Pacific; South East Asia; Western Europe; Eastern Europe; North America; South America; Middle East; Africa
Time Series: Five years historic and ten years forecast.
Data: Ratios of market size and growth to related markets, GDP proportions, expenditure per capita.
Data Segmentation: Country and regional historic and forecast data, market share of competitors, market segments.
Sourcing and Referencing: Data and analysis throughout the report is sourced using end notes.
Delivery Format: Word, PDF or Interactive Report + Excel Dashboard
Added Benefits:
- Bi-Annual Data Update
- Customisation
- Expert Consultant Support
Companies Mentioned
The companies featured in this Security Orchestration market report include:- International Business Machine Corporation
- Palo Alto Networks Inc.
- Fortinet Inc.
- Rapid7 Inc.
- RSA Security LLC
- Exabeam Inc.
- Securonix Inc.
- LogPoint A/S
- Anomali Inc.
- Swimlane
- Cyware Labs Inc.
- Cyberbit Ltd.
- Phantom Cyber
- ThreatConnect Inc.
- Fireeye
- LogRhythm Inc.
- Splunk Inc.
- DFLabs SpA
- Siemplify Ltd.
- Cybersponse Inc.
Table Information
| Report Attribute | Details |
|---|---|
| No. of Pages | 250 |
| Published | March 2026 |
| Forecast Period | 2026 - 2030 |
| Estimated Market Value ( USD | $ 4.76 Billion |
| Forecasted Market Value ( USD | $ 7.76 Billion |
| Compound Annual Growth Rate | 13.0% |
| Regions Covered | Global |
| No. of Companies Mentioned | 21 |