Global Cyber Threat Intelligence Market - Key Trends & Drivers Summarized
How Is Continuous Threat Monitoring Replacing Periodic Security Reviews?
Cyber threat intelligence is transforming security management from scheduled assessment activities into persistent situational awareness driven by constant data analysis. Organizations collect telemetry from endpoints, servers, network devices and cloud services to understand behavior across digital environments. Instead of relying on occasional audits, analytical engines evaluate activity patterns continuously to identify emerging risks. Indicators such as unusual login locations, abnormal data transfers and unexpected process execution are correlated in real time. Security teams observe evolving attack stages rather than isolated alerts allowing early containment actions. Intelligence feeds provide contextual information about attacker techniques enabling faster interpretation of internal signals. Monitoring platforms prioritize events according to potential impact helping analysts focus on critical issues. Historical event comparison reveals gradual changes that traditional rule based systems may overlook. The defensive posture shifts toward proactive vigilance where threats are identified during preparation stages rather than after compromise. Security operations centers therefore operate as intelligence analysis hubs supported by automated observation.Can Behavioral Analytics Reveal Advanced Attack Techniques?
Modern attacks often mimic legitimate activity making signature based detection insufficient for reliable protection. Behavioral analytics models establish baselines for user actions, device communication and application usage patterns across environments. Deviations from expected behavior indicate possible intrusion even when malicious code signatures are unknown. Credential misuse detection identifies lateral movement attempts within networks. Data exfiltration patterns are recognized through correlation of outbound traffic and access frequency anomalies. Privilege escalation attempts are revealed through unusual administrative actions across systems. Continuous learning improves recognition accuracy as organizational activity evolves. Threat hunting teams use analytical queries to explore suspicious relationships between events across time. Machine assisted investigation reconstructs attack sequences to understand tactics and strengthen defenses. The security process evolves into interpretation of intent rather than simple rule matching.How Are Organizations Integrating Intelligence Sharing Into Security Strategy?
Enterprises collaborate with industry partners and intelligence providers to exchange information about emerging attack campaigns and vulnerabilities. Shared threat indicators enrich internal monitoring allowing earlier recognition of coordinated attacks. Security platforms ingest external reports and automatically correlate them with local telemetry. Incident response teams coordinate remediation strategies informed by community experience. Sector specific sharing groups strengthen resilience by distributing knowledge of targeted threats. Government and infrastructure operators integrate national level intelligence to protect critical services. Continuous feedback between organizations improves collective awareness and accelerates defensive adaptation. Training exercises simulate scenarios based on shared intelligence improving preparedness. The security ecosystem becomes interconnected where information exchange enhances overall protection capability.What Factors Are Driving Adoption Of Cyber Threat Intelligence Solutions?
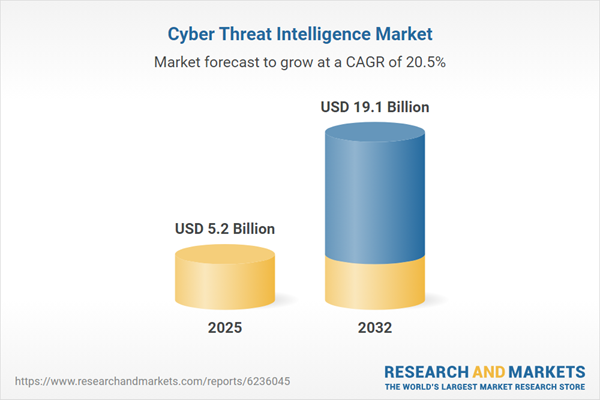
The growth in the Cyber threat intelligence market is driven by several factors including increasing sophistication of attack techniques requiring contextual detection, expansion of digital infrastructure generating extensive security telemetry, and regulatory expectations for proactive risk management. Adoption is also supported by growth of remote work environments expanding attack surfaces, demand for rapid incident response reducing operational disruption, and industry collaboration initiatives encouraging shared defense knowledge. Cloud service adoption necessitates continuous monitoring across distributed systems. Critical infrastructure protection programs require early detection of coordinated threats. Organizations seek automated prioritization to manage alert volume efficiently. These operational and risk management requirements collectively accelerate widespread deployment of intelligence driven cybersecurity capabilities across modern enterprises.Report Scope
The report analyzes the Cyber Threat Intelligence market, presented in terms of market value (US$). The analysis covers the key segments and geographic regions outlined below:- Segments: Component (Solutions Component, Services Component); Deployment (Cloud Deployment, On-Premise Deployment); Type (Operational Intelligence Type, Tactical Intelligence Type, Strategic Intelligence Type); End-Use (BFSI End-Use, Government & Defense End-Use, IT & Telecom End-Use, Healthcare & Life Sciences End-Use, Other End-Uses)
- Geographic Regions/Countries: World; USA; Canada; Japan; China; Europe; France; Germany; Italy; UK; Rest of Europe; Asia-Pacific; Rest of World.
Key Insights:
- Market Growth: Understand the significant growth trajectory of the Solutions Component segment, which is expected to reach US$10.2 Billion by 2032 with a CAGR of a 18.1%. The Services Component segment is also set to grow at 23.9% CAGR over the analysis period.
- Regional Analysis: Gain insights into the U.S. market, valued at $1.5 Billion in 2025, and China, forecasted to grow at an impressive 19.6% CAGR to reach $3.2 Billion by 2032. Discover growth trends in other key regions, including Japan, Canada, Germany, and the Asia-Pacific.
Why You Should Buy This Report:
- Detailed Market Analysis: Access a thorough analysis of the Global Cyber Threat Intelligence Market, covering all major geographic regions and market segments.
- Competitive Insights: Get an overview of the competitive landscape, including the market presence of major players across different geographies.
- Future Trends and Drivers: Understand the key trends and drivers shaping the future of the Global Cyber Threat Intelligence Market.
- Actionable Insights: Benefit from actionable insights that can help you identify new revenue opportunities and make strategic business decisions.
Key Questions Answered:
- How is the Global Cyber Threat Intelligence Market expected to evolve by 2032?
- What are the main drivers and restraints affecting the market?
- Which market segments will grow the most over the forecast period?
- How will market shares for different regions and segments change by 2032?
- Who are the leading players in the market, and what are their prospects?
Report Features:
- Comprehensive Market Data: Independent analysis of annual sales and market forecasts in US$ Million from 2025 to 2032.
- In-Depth Regional Analysis: Detailed insights into key markets, including the U.S., China, Japan, Canada, Europe, Asia-Pacific, Latin America, Middle East, and Africa.
- Company Profiles: Coverage of players such as Anomali Inc., AO Kaspersky Lab, Check Point Software Technologies Ltd., Cisco Systems, Inc., Crowdstrike, Inc. and more.
- Complimentary Updates: Receive free report updates for one year to keep you informed of the latest market developments.
Some of the companies featured in this Cyber Threat Intelligence market report include:
- Anomali Inc.
- AO Kaspersky Lab
- Check Point Software Technologies Ltd.
- Cisco Systems, Inc.
- Crowdstrike, Inc.
- Dataminr
- Fortinet, Inc.
- Group-IB
- IBM Corporation
- Intel 471
Domain Expert Insights
This market report incorporates insights from domain experts across enterprise, industry, academia, and government sectors. These insights are consolidated from multilingual multimedia sources, including text, voice, and image-based content, to provide comprehensive market intelligence and strategic perspectives. As part of this research study, the publisher tracks and analyzes insights from 43 domain experts. Clients may request access to the network of experts monitored for this report, along with the online expert insights tracker.Companies Mentioned (Partial List)
A selection of companies mentioned in this report includes, but is not limited to:
- Anomali Inc.
- AO Kaspersky Lab
- Check Point Software Technologies Ltd.
- Cisco Systems, Inc.
- Crowdstrike, Inc.
- Dataminr
- Fortinet, Inc.
- Group-IB
- IBM Corporation
- Intel 471
Table Information
| Report Attribute | Details |
|---|---|
| No. of Pages | 212 |
| Published | May 2026 |
| Forecast Period | 2025 - 2032 |
| Estimated Market Value ( USD | $ 5.2 Billion |
| Forecasted Market Value ( USD | $ 19.1 Billion |
| Compound Annual Growth Rate | 20.5% |
| Regions Covered | Global |